 Why is my computer so slow? We got this question often in our comments section, so we are dedicating a reference article on this subject. When I asked myself this question Why is my computer so slow? for the first time, I did not have much understanding of computers at that point. It were the days that virus issues became a big deal. My computer was infected, pleas do’nt laugh, with the Pikachu virus, sometimes referred to as Pokey Virus. It was a really silly virus geared at children due to its incorporation of Pikachu from the Pokémon series. I got it in the form of an e-mail titled “Pikachu Pokemon [sic]” with the subject “Pikachu is your friend.” There was an attachment included and of course I opened it ) : As a consequence my computer was infected and became slow.
Why is my computer so slow? We got this question often in our comments section, so we are dedicating a reference article on this subject. When I asked myself this question Why is my computer so slow? for the first time, I did not have much understanding of computers at that point. It were the days that virus issues became a big deal. My computer was infected, pleas do’nt laugh, with the Pikachu virus, sometimes referred to as Pokey Virus. It was a really silly virus geared at children due to its incorporation of Pikachu from the Pokémon series. I got it in the form of an e-mail titled “Pikachu Pokemon [sic]” with the subject “Pikachu is your friend.” There was an attachment included and of course I opened it ) : As a consequence my computer was infected and became slow.
Here we have a first answer on the question – Why is my computer so slow?: malware infections!
The Pikachu was quite an innocent virus compared to what we are confronted with theses days on the internet. The increase of particularly spyware is quite troublesome. Spyware is developped in order to avoid detection and has many tricks in its sleaves to fool antivirus products. In fact, well developped spyware has many components as well and should be called modular malware. Potentially, it could do many different stuff on your computer, without you noticing it, like installing a keylogger or a rootkit and turning it into a so called zombie computer. A zombie computer is completely under the control of a hacker and organized in networks in order to attack on a certain time a certain target, for example a bank. Anyhow, many people are working on a slow computer because as soon as it connects to the internet it is communicating with the server of the hacker. For example, spyware could share all privacy sensitive data with the server of the hacker in search for credit card details and other details that would enable a cybercriminal to steal some real cash. If there is nothing to find, the cyber criminal might decide to install a ransomware program to lock your computer and force you to pay a X sum of money in order to get your computer unlocked.
 Is your internet slow and does your computer slow down in perfomance as soon it connects to the internet? To be honest, almost all users underestimate the risks and overestimate their own situation. Did you know that most antivirus products are completely inadequate to protect you from all possible malware attacks on the internet? It is strongly recommended to use a second-opinion malware scanner in order to double check if your slow computer has no spyware or rootkits active on your system.
Is your internet slow and does your computer slow down in perfomance as soon it connects to the internet? To be honest, almost all users underestimate the risks and overestimate their own situation. Did you know that most antivirus products are completely inadequate to protect you from all possible malware attacks on the internet? It is strongly recommended to use a second-opinion malware scanner in order to double check if your slow computer has no spyware or rootkits active on your system.
Double check your system with the SpyHunter or the Hitman Pro. These programs are real specialists and have a proven track record as excellent spyware removal tools and rootkit scanners. Forget not to invest in the best internet security for protecting yourself online. We are these days completely dependent on the internet and your computers. Cybercriminals know this and operate international to earn money on us as possible malware victims. Are you using a mac? Then I would recommend you read my article on mac antivirus software.
2. Why is my computer so slow?: you did not take care of it!
Besides possible malware infections,there could be less problematic issues at the root of your problem with your computer. The question why is my computer so slow? is raised because of frustration about not knowing what is causing this system slow down. The computer is a complex mixture of apps, software and hardware with some set limitations on performance and bandwith. All the diferent hardware and software components need to communicate effictely with eachother. The problem is that software vendors are regularly forcing us to update software components that might effect the communication with for example hardware components. Here we have the so called software driver issues. Outdated drivers might be responsible for why your computer is so slow. This in combination with bloathed hard disks and stuffed internet browers and too many active programs claiming all your system resources could easily slow down your computer.
 It is not easy to know what exaclty is causing the problem. Therefore have many software companies worked on the development of complete utility software programs for analysing slow computers. The reason I bring this up is that on the internet there are many different programs available that deal only with 1 possible cause for a slow system. For example, the Windows registry could be riddled with obsolete and corrupt registry keys after a malware indicent. To repair and clean the Windows registry would have a great impact on system performance and stability. Nevertheless, we only have dealed with one compontent of your computer, a damaged registry. What about the fragmented hard disk that is causing slow downs? Are you going to buy a registry cleaner and a driver cleaner seperately? What about your updated drivers? Are you going to wait with this problem and buy a driver scanner when the problem is more prevelant? No, of course not, we shoud invest in a complete all-in-one program for cleaning, optimizing and repairing all components of your computer. I did a lot of research on finding all-in-one computer care programs developped by Microsoft Certified Vendors. Here is my list of the best programs availble. I would recommend you download one of these to check your computer on issues and errors that are slowing down your system.
It is not easy to know what exaclty is causing the problem. Therefore have many software companies worked on the development of complete utility software programs for analysing slow computers. The reason I bring this up is that on the internet there are many different programs available that deal only with 1 possible cause for a slow system. For example, the Windows registry could be riddled with obsolete and corrupt registry keys after a malware indicent. To repair and clean the Windows registry would have a great impact on system performance and stability. Nevertheless, we only have dealed with one compontent of your computer, a damaged registry. What about the fragmented hard disk that is causing slow downs? Are you going to buy a registry cleaner and a driver cleaner seperately? What about your updated drivers? Are you going to wait with this problem and buy a driver scanner when the problem is more prevelant? No, of course not, we shoud invest in a complete all-in-one program for cleaning, optimizing and repairing all components of your computer. I did a lot of research on finding all-in-one computer care programs developped by Microsoft Certified Vendors. Here is my list of the best programs availble. I would recommend you download one of these to check your computer on issues and errors that are slowing down your system.
 The Mackeeper Human Inside is a new feature included in the Mackeeper 3.x version released in 2015. Kromtech has worked hard to develop this feature which adds quite some value to the Mackeeper software.
The Mackeeper Human Inside is a new feature included in the Mackeeper 3.x version released in 2015. Kromtech has worked hard to develop this feature which adds quite some value to the Mackeeper software.  Thus, every MacKeeper 3 User Has 24/7 Access To Apple Certified Support Professionals. You can consider them as your personal assistant who has the solution for your technical problem.
Thus, every MacKeeper 3 User Has 24/7 Access To Apple Certified Support Professionals. You can consider them as your personal assistant who has the solution for your technical problem. 
 Since then the
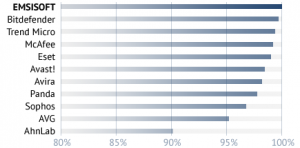
Since then the  The current Emsisoft anti-malware 9.0 software is an excellent, super powerful dual malware scanner. You could compare it with the Hitman Pro of SurfRight. Surfright is as well a very innovative security software company. The advantage Emsisoft has is the fact it has a tactical technological partnership with Bitdefender. Bitdefender and Kaspersky are amongst the best security software brands and score always very high in comparative tests. Nevertheless, the Emsisoft Anti-Malware 9.0 software is much cheaper!
The current Emsisoft anti-malware 9.0 software is an excellent, super powerful dual malware scanner. You could compare it with the Hitman Pro of SurfRight. Surfright is as well a very innovative security software company. The advantage Emsisoft has is the fact it has a tactical technological partnership with Bitdefender. Bitdefender and Kaspersky are amongst the best security software brands and score always very high in comparative tests. Nevertheless, the Emsisoft Anti-Malware 9.0 software is much cheaper! The research lab of Enigma Software, the maker of the
The research lab of Enigma Software, the maker of the  One of the best tools you could use is the second-opinion malware scanner of Surfright, the
One of the best tools you could use is the second-opinion malware scanner of Surfright, the  Well do not worry too much! As you can read in the article:
Well do not worry too much! As you can read in the article: 




 1. During a comparative Malware Detection Test of AV-TEST
1. During a comparative Malware Detection Test of AV-TEST 
 Most antivirus programs and internet security suites are not able to detect all malware. You are never 100 % secured against all possible attack vectors and new malware species, mutations and variations. For example, banking Trojans are very difficult to detect, even with up-to-date antivirus software. This is because the attackers use custom-engineered binary obfuscation (polymorphism), cloaking and other armoring techniques to evade detection the first few days. To maximize the effectiveness of their campaign they test each specially crafted malware sample against antivirus products. That’s why everybody should use a second-opinion malware scanner.
Most antivirus programs and internet security suites are not able to detect all malware. You are never 100 % secured against all possible attack vectors and new malware species, mutations and variations. For example, banking Trojans are very difficult to detect, even with up-to-date antivirus software. This is because the attackers use custom-engineered binary obfuscation (polymorphism), cloaking and other armoring techniques to evade detection the first few days. To maximize the effectiveness of their campaign they test each specially crafted malware sample against antivirus products. That’s why everybody should use a second-opinion malware scanner. There are many people looking to install legimately spy software on computers, mobiles and smart phones. A program that works as your own internet spy to monitor all devices. So,
There are many people looking to install legimately spy software on computers, mobiles and smart phones. A program that works as your own internet spy to monitor all devices. So,  In that case you should use the Mspy.
In that case you should use the Mspy. 
 Although the use of spy software is not always illegimate, it is a violation of your
Although the use of spy software is not always illegimate, it is a violation of your


 There are many cheesy, half-baked solutions that are supposed to help you to become more safe and anonymous on the internet. In particular, the
There are many cheesy, half-baked solutions that are supposed to help you to become more safe and anonymous on the internet. In particular, the  Anonymous surfing is only possible if you apply the best internet security measures in order to make sure you do not get infected with malicious programs or keylogger programs of third parties. Before you start to implement your new online surfing strategy, make sure your computer is clean from possible spyware hiding on your system. For more information:
Anonymous surfing is only possible if you apply the best internet security measures in order to make sure you do not get infected with malicious programs or keylogger programs of third parties. Before you start to implement your new online surfing strategy, make sure your computer is clean from possible spyware hiding on your system. For more information:  The best internet security is not just a question of buying the best internet security software. Identity theft and
The best internet security is not just a question of buying the best internet security software. Identity theft and  Of course, the installation of great internet security solution is a necessary step. This is applicable for Mac systems as well. Mac users should also invest in an internet security solution. The
Of course, the installation of great internet security solution is a necessary step. This is applicable for Mac systems as well. Mac users should also invest in an internet security solution. The  This brings us to our best internet security tip and measure you should take. Please, install the Secunia Personal Software Inspector. This is a free security tool which assists you in making sure all your applications and software programs installed on your computer are up-to-date. The Secunia PSI ensures your programma’s are not vulnerable anymore. This is a very important pre-emptive internet security measure which will make sure hidden malware programs on websites are not able to attack your computer. For more information:
This brings us to our best internet security tip and measure you should take. Please, install the Secunia Personal Software Inspector. This is a free security tool which assists you in making sure all your applications and software programs installed on your computer are up-to-date. The Secunia PSI ensures your programma’s are not vulnerable anymore. This is a very important pre-emptive internet security measure which will make sure hidden malware programs on websites are not able to attack your computer. For more information: 